11. Sınıf Meb Yayınları İngilizce Ders Kitabı Sayfa 61 Cevabı

“11. Sınıf Meb Yayınları İngilizce Ders Kitabı Sayfa 61 Cevapları” ulaşabilmek ve dersinizi kolayca yapabilmek için aşağıdaki yayınımızı mutlaka inceleyiniz.
11. Sınıf Meb Yayınları İngilizce Ders Kitabı Sayfa 61 Cevabı
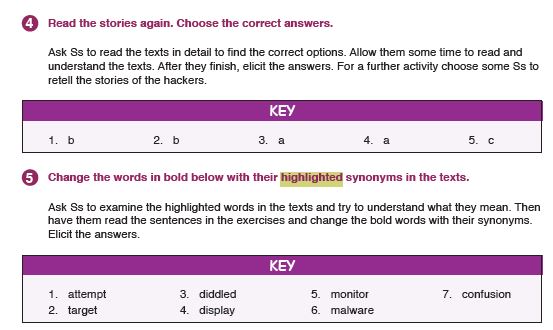
Read the stories again. Choose the correct answers.
1. Cyber criminals sometimes……..
a) make people believe in their methods
b) want people to watch and follow them
c) earn a lot while sneaking into systems
2. Marcony’s rival set up a plan to……..
a) steal the method of Marconi’s device
b) make fun of his rival
c) write an insulting poem
3. Intelligence service of a country……..
a) attacked the computer systems for fun
b) changed the system to learn nuclear facilities
c) wanted to play rock&roll at night
4. While drivers were on the road in San
Francisco,……..
a) they saw an extraordinary road sign
b) they saw a Godzilla attack
c) they had serious accidents because of a road sign
5. The hackers………
a) sold the fast food company to its rival
b) didn’t let the owners take the account back
c) stole the account although the company was one of the big ones
[5) Change the words in bold below with their highlighted synonyms in the texts.
1. They tryto enlarge the company he inherited from his grandfather.___
2. Harry’s main goal is to operate computer systems professionally._____
3. In 1990s some bankers cheated public with high incomes.__________
4. The layout of my account is a pigeon and an olive branch.__________
5. Hackers keep an eye on the programme to steal information.________
6. Hackers design harmful software to steal the information of the people.
7. Misunderstanding the departure time caused a deep chaos.________
………………………………………………….
Sometimes cyberattacks affect whole public. Once the taı-get of the hackers was all the roads. But how?
In 2014 some hackers sneaked into the electronic signs in San Frandsco. They changed the messages on the road signs. When the people driving on these roads came across the sign written GODZILLA ATTACK – TURN BACK, they didn’t know what to d° or where to drive. This caused lots of confusion. The good part of the story was this didn’t cause any ^dtente.
D…………………………..
Cyber attacks aren’t usually made by ordinary hackers. Most governments have launched professional systems to monitor the facilities of their enemies or rivals. They have been operating this to get information about the secrets of other countries. |n 2012 intelligence service of a country sent a worm to the control system of several nuclear works of their rival country. But this time they just wanted to have a good laugh. The malware turned off the monitoring stations and other hardware. Several times during the night it started work-stations and made them play rock
music at maximum volume. It really left the system operators in y
panic until they could solve the problem.
- Cevap:
“11. Sınıf İngilizce Ders Kitabı Cevapları Meb Yayınları Sayfa 61” ile ilgili aşağıda bulunan emojileri kullanarak duygularınızı belirtebilir aynı zamanda sosyal medyada paylaşarak bizlere katkıda bulunabilirsiniz.